2022 | UGRACTF | CRYPTO
noteasy03
题目¶
Цезарь скривился,
Замкнулся в себе.
Преумножение.
Caesar curved, closed in on himself. Multiplication.
解题思路 English ver.¶
- 根据题目
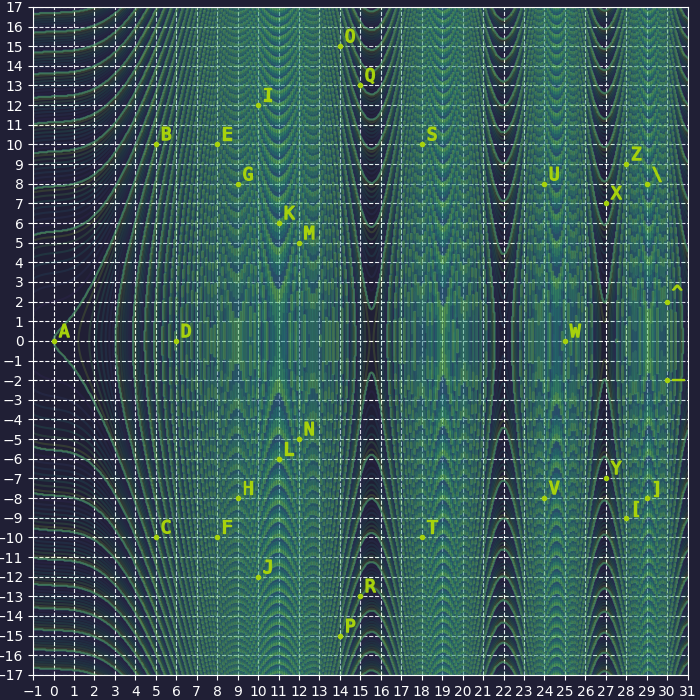
curved/closed in on himself和图片,推测应该是某种曲线,且所有点在曲线上都能找到对应点 -
分析密文,结合
flag的格式,得到以下映射关系。再结合Caesar推测是单表代换 -
排除常见的单表代换密码(都是线性的),最后想到了椭圆曲线
- 尽管点分布的形状似乎和实数域的椭圆曲线不搭边,但若考虑是在有限域,则图中点集完全符合有限域中椭圆曲线的特性
- 同时,椭圆曲线上点的逆元可以符合加解密的映射需求
- 根据各点坐标大小可推出有限域大小为 \(31\)
- 通过 在线椭圆曲线可视化工具 寻找椭圆曲线系数的大致范围
- 关键特征:三个点位于 \(x\) 轴,一个点位于 \((0, 0)\)
-
再结合有限域和已知点的坐标确定椭圆曲线系数 \(a=-5,b=0\)
-
根据
Caesar和Multiplication推测点的映射为椭圆曲线中的点乘,系数为 \(3\),然而解密的结果是一堆乱码 :( -
最早的凯撒密码为移 \(3\) 位,后来扩展为移位密码。于是尝试改变系数,当系数为 \(11\) 时成功获得 Flag XD
Flag¶
ugra_in_case_of_losing_your_sanity_dial_oh_three_oijnacjfhjaghhcajgfcd
最后更新:
2022年4月22日 23:55:03
Contributors: